Exploiting a PHP Object Injection in Profile Builder Pro in the era of AI
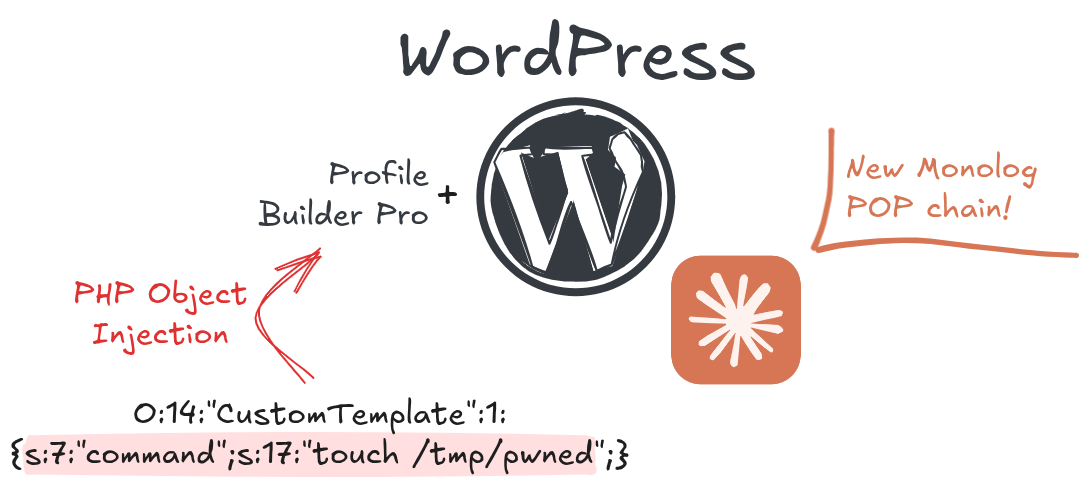
WordPress plugin "Profile Builder Pro" (versions before 3.14.5) is susceptible to Unauthenticated PHP Object Injection. In this blog post, we discuss how we discovered and exploited the vulnerability using a novel POP chain, how AI helped in the process, taking a final look at targets in the wild.
Summary
- Product
- Profile Builder Pro
- Vendor
- Cozmoslabs
- Affected Version(s)
- 3.14.5 and below
- First Patched Version
- 3.14.6
- Impact
- The vulnerability allows an arbitrary PHP object to be injected into memory, which is then deserialized without being checked. The impacts depend heavily on the presence of useful gadgets within other plugins. In our case, we exploited a novel Monolog POP chain within the ‘The-Event-Calendar’ plugin to deploy our web shell and achieve remote code execution.
Abstract
WordPress plugin Profile Builder Pro (versions before 3.14.5) is susceptible to Unauthenticated PHP Object Injection. In this blog post, we discuss how we discovered and exploited the vulnerability using a novel POP chain discovered inside another plugin, how AI helped in the process, taking a final look at targets in the wild.
You can read the full article on the SicuraNext blog.
This post is licensed under
CC BY 4.0
by the author.